Broken Authentication: What It Is and How to Stop It
admin
13 March, 2026Every 39 seconds, a cyberattack happens somewhere on the internet — and broken authentication is one of the most exploited entry points. In 2025 alone, attacks targeting authentication vulnerabilities surged by 45%, making it one of the fastest-growing threat vectors in cybersecurity. Yet despite its severity, broken authentication often goes undetected until a breach has already caused irreversible damage. This article breaks down exactly what broken authentication is, how attackers exploit it, and — most importantly — what your organization can do to stop it. From real-world breach cases to step-by-step hardening strategies, you’ll walk away with actionable insight. We’ll also explore how tools like GenLogin are redefining what secure, multi-account authentication management looks like in practice.
Table of Contents
ToggleUnderstanding Broken Authentication
Broken authentication isn’t a single vulnerability — it’s an umbrella term for a category of flaws that allow attackers to bypass login mechanisms and impersonate legitimate users. In 2025, weak or stolen passwords were implicated in 81% of data breaches, a figure that has remained stubbornly high despite years of industry warnings. The persistence of this problem isn’t a matter of ignorance; it’s a matter of implementation. Organizations know passwords are weak. Many simply haven’t replaced them with something stronger.
At its core, broken authentication exploits three systemic gaps: weak password policies that users can easily circumvent, session management flaws that let attackers hijack active sessions, and poorly configured multi-factor authentication (MFA) that provides false reassurance. Each of these gaps represents a different attack surface — and sophisticated threat actors know how to target all three simultaneously.
A vivid example came in 2024, when a major social media platform suffered a large-scale breach traced back to a flawed password recovery flow. Attackers didn’t need to crack passwords — they simply exploited the recovery mechanism itself, bypassing authentication entirely. Millions of accounts were compromised. The aftermath included regulatory fines, a wave of user churn, and months of reputation repair. The breach wasn’t caused by a zero-day exploit or nation-state tooling. It was caused by a broken process that should have been caught in a security audit years earlier.
The takeaway is uncomfortable but important: broken authentication is largely preventable. Strong password policies, secure session management, and properly deployed MFA can eliminate the vast majority of these attack vectors. The gap isn’t knowledge — it’s execution.
Common Vulnerabilities in Authentication Systems
Authentication systems are only as strong as their weakest component, and attackers are methodical about finding it. Three vulnerabilities consistently appear at the top of breach post-mortems: weak password policies, session fixation and hijacking, and inadequate MFA implementation.
Weak passwords remain the most exploited vulnerability in existence — not because defenders don’t know about them, but because enforcing strong password hygiene at scale is genuinely difficult. Users resist complexity. They reuse passwords across platforms. They store them insecurely. Attackers capitalize on this through brute force attacks (automated password guessing using common patterns) and credential stuffing (replaying username/password pairs stolen from previous breaches). Once one account falls, lateral movement becomes trivially easy — especially when users have reused the same credentials elsewhere.
Session fixation and hijacking represent a more technical, but equally dangerous, attack class. In session fixation, an attacker manipulates a user’s session ID before they authenticate, effectively pre-positioning themselves for access the moment the user logs in. Session hijacking skips that step entirely — the attacker steals an active session token through packet sniffing, cross-site scripting (XSS), or man-in-the-middle interception, then uses it to impersonate the user without ever needing their credentials. The result in both cases is unauthorized access that can be nearly invisible to the victim.
Inadequate MFA is perhaps the most insidious vulnerability because it creates a false sense of security. Organizations that deploy MFA believe they’re protected — but if that MFA relies solely on SMS verification, they remain exposed to SIM-swapping attacks, where threat actors socially engineer mobile carriers into transferring a victim’s phone number to an attacker-controlled SIM. The authentication code arrives — just to the wrong person.
Addressing these vulnerabilities requires more than policy updates. It requires a layered approach: enforced password complexity, secure session lifecycle management, and MFA methods that don’t depend on easily intercepted channels.
Exploiting Weak Password Policies
Attackers don’t guess passwords manually — they automate the process at scale. Brute force tools can test thousands of password combinations per second, while credential stuffing tools weaponize leaked databases containing billions of real username/password pairs from previous breaches. The economics are in the attacker’s favor: running these attacks costs almost nothing, and even a 0.1% success rate across a million accounts yields thousands of compromised credentials.
The cascading impact of password reuse makes this worse. A user whose gaming forum credentials are leaked may not consider it a serious event — until those same credentials unlock their work email, their cloud storage, or their financial accounts. Poor password storage practices on the service provider’s end amplify the damage further: plaintext or weakly hashed passwords hand attackers a ready-to-use credential list rather than forcing them to crack anything.
Mitigation requires action on multiple fronts. Organizations should enforce minimum password complexity requirements and block the reuse of previous passwords. Password storage must use modern hashing algorithms (bcrypt, Argon2) with appropriate salting. And users need practical tools — password managers eliminate the cognitive burden of remembering complex, unique passwords, removing the incentive to reuse them in the first place.
Understanding Session Hijacking
Session hijacking is effective precisely because it sidesteps the credential problem altogether. Once a user is authenticated, their session is maintained through a token — a unique identifier that the server uses to recognize them across requests. An attacker who obtains that token doesn’t need to know the user’s password. They simply present the token, and the server treats them as the legitimate user.
Token theft happens through multiple vectors: XSS payloads that exfiltrate cookies, packet sniffing on unencrypted connections, and phishing pages that capture session data in transit. The consequences scale with the privilege level of the hijacked session. On an e-commerce platform, a hijacked session might mean fraudulent purchases. On an enterprise application, it could mean unauthorized access to customer data, internal systems, or administrative controls.
Prevention centers on making tokens harder to steal and shorter-lived when stolen. HTTPS should be non-negotiable — it encrypts traffic in transit, eliminating passive sniffing as an attack vector. Session cookies should be flagged HttpOnly (preventing JavaScript access) and Secure (preventing transmission over unencrypted connections). Token lifetimes should be short, with re-authentication required for sensitive operations. And user education on recognizing phishing attempts provides a human layer of defense that technical controls alone can’t replicate.
Case Study: The Impact of Broken Authentication
In 2024, a major financial institution learned the cost of deferred authentication upgrades the hard way. Attackers exploited aging, single-factor authentication systems to gain unauthorized access to sensitive customer records. The systems in question lacked MFA entirely — a known gap that had been on the security team’s roadmap but hadn’t been prioritized. By the time the breach was detected, the damage was done.
The organization’s response was swift and methodical. Rather than deploying MFA across all systems simultaneously — a move that risks disruption and inconsistent implementation — they adopted a phased rollout. High-risk accounts (administrative users, privileged roles) were migrated first, allowing the security team to identify integration issues and refine the deployment process before extending it to the broader user base. This approach proved effective: the controlled rollout caught several compatibility issues with legacy systems that a rushed, organization-wide deployment would have missed.
Alongside the technical remediation, the organization invested heavily in employee training. This wasn’t checkbox compliance training — it was targeted education focused on phishing recognition, the specific social engineering tactics used in the breach, and the role each employee plays in the authentication chain. Security tools are only as effective as the people using them, and the training addressed that human layer directly.
The results validated the approach. Unauthorized access attempts dropped significantly in the months following MFA deployment. The comprehensive security audit that ran in parallel with the rollout uncovered additional vulnerabilities — hardcoded credentials in legacy applications, overly permissive session timeouts — that were remediated before they could be exploited.
The broader lesson from this case isn’t just “implement MFA.” It’s that authentication security requires ongoing investment, not one-time fixes. Threat actors adapt. Authentication systems age. What’s secure today may be insufficient next year. The organizations that weather these threats consistently are those that treat authentication security as a continuous process rather than a project with a completion date.
Implementing Strong Authentication Solutions
With stolen credentials implicated in approximately 61% of breaches, password-based authentication alone is not a defensible security posture. The shift to strong authentication isn’t optional — it’s a prerequisite for operating securely in a threat environment where credential theft is industrialized. MFA is the cornerstone of that shift, but effective implementation requires more than flipping a switch.

-
Evaluate Current Systems:
Before deploying anything new, conduct a thorough audit of existing authentication processes. Map every access point, identify which systems lack MFA, analyze user access patterns for anomalies, and document potential attack vectors. You can’t secure what you haven’t fully inventoried. -
Select Appropriate MFA Methods:
Not all MFA is created equal. SMS-based verification is better than nothing, but it’s vulnerable to SIM-swapping. Authenticator apps (TOTP-based) offer stronger protection and don’t depend on carrier security. Hardware tokens and biometric systems provide the highest assurance levels but come with hardware requirements and enrollment complexity. Choose methods that match both your threat model and your users’ practical ability to adopt them. -
Integrate MFA into Existing Systems:
Deploy MFA across all access points — not just the most obvious ones. Legacy applications, internal tools, and API endpoints are frequently overlooked and disproportionately targeted. Ensure the integration is tested thoroughly before going live, particularly for systems with older authentication frameworks. -
Educate Users:
Technical controls fail when users don’t understand them. Provide clear, practical training that explains why MFA matters, how to use it correctly, and what to do if something seems off (unexpected authentication prompts, suspicious login notifications). Resistance to MFA often stems from confusion, not malice — good onboarding resolves most of it. -
Monitor and Adjust:
Authentication security isn’t static. Monitor authentication logs for anomalies — repeated failed attempts, logins from unusual locations, rapid account switching — and tune your detection thresholds accordingly. As threat tactics evolve, your authentication configuration needs to evolve with them.
MFA is the foundation, but a mature authentication strategy layers additional controls on top: risk-based authentication that escalates verification requirements when behavior looks anomalous, zero-trust architecture that validates every access request regardless of network location, and regular penetration testing that probes authentication systems before attackers do.
Multi-Factor Authentication: A Key Defense
The numbers behind MFA are striking: approximately 99.9% of automated account compromise attacks are blocked when MFA is in place. That figure reflects a fundamental reality — most large-scale attacks are opportunistic and automated. They exploit easy targets. MFA raises the cost of attack to the point where opportunistic actors move on.
The mechanism is straightforward: MFA requires at least two independent factors — something you know (a password), something you have (a phone or hardware token), and something you are (a biometric). Compromising one factor doesn’t grant access. An attacker with a stolen password still needs the second factor, which they typically don’t have. This breaks the credential theft attack chain at a critical point.
The challenges in MFA deployment are real but solvable. User friction is the most common barrier — additional steps slow down login, and users often push back. The solution is choosing friction-appropriate methods. Push notification-based MFA (where users simply tap “Approve” on their phone) adds minimal friction while providing strong protection. Biometric authentication — fingerprint or face recognition — is often faster than typing a password. Framing MFA as a convenience upgrade rather than a security inconvenience can shift user perception significantly.
A financial services firm implementing biometric MFA found initial resistance from users unfamiliar with the technology. A structured rollout with clear instructional materials and a brief hands-on demo period resolved most objections within two weeks. Post-deployment, unauthorized access attempts against the firm’s systems dropped measurably — and users who had resisted the change became its advocates once they experienced how seamless it was.
MFA deployment should be treated as a milestone, not a destination. Continuously monitor effectiveness, stay current on emerging bypass techniques (MFA fatigue attacks, real-time phishing proxies), and update your MFA strategy accordingly.
GenLogin: Enhancing Authentication Security Through Advanced Profiling
For individuals and organizations managing multiple accounts across platforms, authentication security takes on an additional dimension: not just protecting access, but ensuring that multiple identities remain cleanly separated and operationally secure. This is where GenLogin delivers capabilities that conventional authentication tools simply don’t address.
GenLogin’s core strength lies in its advanced browser profiling engine. Each profile created in GenLogin operates as a fully isolated digital environment — distinct browser fingerprint, dedicated proxy assignment, separate cookie storage, and independent session state. This isolation is critical from a security standpoint: over 60% of authentication breaches are linked to insufficient session isolation, where data or session tokens bleed between accounts. GenLogin’s architecture eliminates that cross-contamination risk by design.
The proxy management layer adds another security dimension. GenLogin assigns unique IP addresses to each profile, ensuring that multiple accounts operated from the same machine appear to originate from distinct, geographically appropriate locations. This matters not just for platform compliance — it directly addresses one of the most common authentication red flags that security systems use to detect account takeover: sudden IP inconsistencies. By maintaining consistent, profile-specific IP associations, GenLogin prevents the kind of anomalous login patterns that trigger account locks or security reviews.
For a digital marketing agency managing campaigns across dozens of client accounts, GenLogin’s impact is operational as well as security-focused. Each client’s accounts live in a fully isolated profile — no shared cookies, no overlapping fingerprints, no risk of one client’s session data contaminating another’s. The agency can automate routine tasks (posting, monitoring, reporting) across profiles simultaneously without triggering platform detection systems. The result is both stronger security and meaningfully higher operational throughput.
To get the most from GenLogin’s security capabilities, users should treat proxy hygiene as an ongoing practice: regularly rotate proxies where platform policies require it, verify proxy health before sensitive operations, and use GenLogin’s session monitoring dashboard to spot anomalous activity early. GenLogin doesn’t just make multi-account management possible — it makes it auditable and defensible.
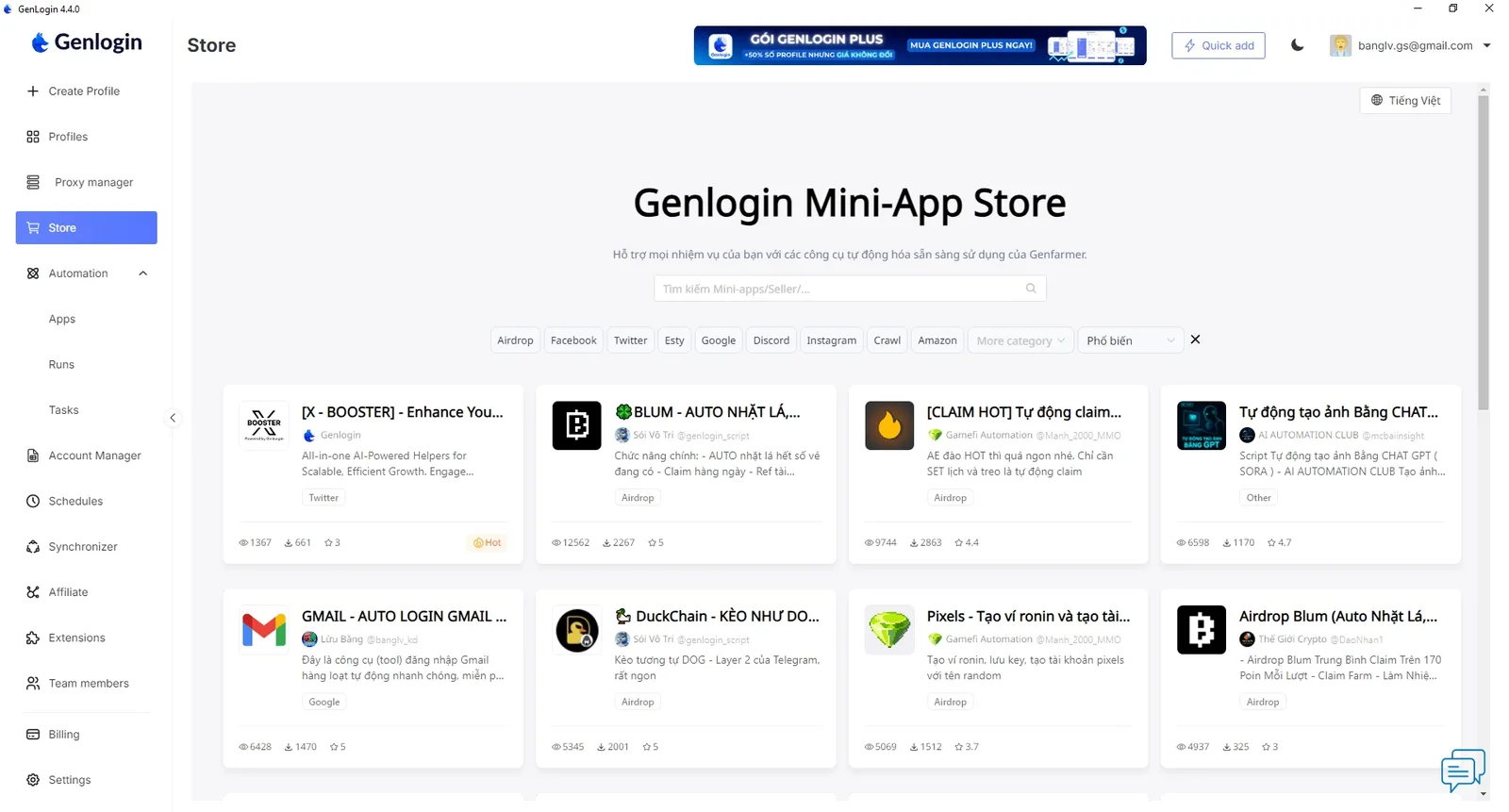
Leveraging GenLogin for Secure Multi-Account Management
Multi-account management is a legitimate operational requirement for social media managers, e-commerce operators, digital marketers, and affiliate marketers — but it introduces authentication risks that standard security tools aren’t designed to handle. GenLogin was built specifically for this use case, and its feature set reflects a deep understanding of how multi-account environments fail.
The core workflow is straightforward: each account gets its own GenLogin profile, configured with a dedicated proxy and isolated browser environment. A social media manager handling ten brand accounts creates ten profiles. Each operates independently — no shared sessions, no common fingerprints, no IP overlap. Platforms that actively detect and ban multi-account usage see each profile as a distinct, legitimate user. The operational risk of account bans due to shared IP usage drops to near zero.
A digital marketing firm using GenLogin to manage multi-client campaigns reported concrete results: campaign management time decreased as automation scripts could run across profiles simultaneously, account-related suspensions dropped significantly, and client data remained cleanly separated with no crossover incidents. The firm’s account managers described the transition as moving from “constantly firefighting account bans” to “running a predictable, scalable operation.”
Best practices for GenLogin in multi-account environments include: aligning proxy geography with each account’s registration location, regularly auditing profile configurations to ensure fingerprint uniqueness, and using GenLogin’s analytics features to monitor session behavior across all profiles from a single dashboard. For teams, GenLogin’s profile-sharing capabilities allow secure handoffs between team members without exposing underlying credentials — each user accesses the profile through GenLogin’s controlled environment rather than directly handling login credentials.
In environments where authentication security and operational efficiency are both non-negotiable, GenLogin provides a single platform that addresses both — without forcing a trade-off between the two.
Conclusion
Broken authentication is not an emerging threat — it’s a persistent, well-documented vulnerability that continues to power the majority of significant data breaches. With 81% of 2025 breaches tied to weak or stolen credentials, and 61% of all breaches involving credential theft, the data is unambiguous: authentication is where attackers focus, and it’s where defenders must respond with equal intensity.
The 2024 financial institution breach illustrates what happens when authentication remediation is deferred — and what’s possible when organizations respond decisively. MFA deployment, comprehensive auditing, and targeted user education transformed a reactive incident response into a proactive security posture. That transformation is replicable, but it requires commitment and the right tools.
For organizations operating across multiple accounts, platforms, or digital identities, GenLogin addresses a layer of authentication security that conventional tools overlook — session isolation, IP consistency, fingerprint separation, and auditable multi-account management. It’s not a replacement for MFA or strong password policies; it’s a complement that secures the operational layer where those controls would otherwise fall short.
Authentication security is not a project you complete — it’s a capability you build and continuously maintain. Start with the fundamentals: enforce strong passwords, deploy MFA, manage sessions securely. Then layer in tools that address your specific operational context. Visit GenLogin Market to explore scripts and solutions built for secure, scalable multi-account operations — and take the next step toward authentication security that actually holds up under real-world conditions.
Try Free Trial
Don’t forget you have free 5 profiles
Try it first and love it later!


JOINT STOCK COMPANY GENLOGIN SOFTWARE
Address: 275 Nguyen Trai, Thanh Xuan, Hanoi (Huy Hoang building)